Installation¶
Installing the product on the workstation¶
Installation on different platforms is described in the installation guide .
Application configuration¶
Applications using Windows interfaces (CryptoAPI / Microsoft CNG)¶
These applications (typically Edge, Chrome, Microsoft office tools, etc.) require no special configuration. The certificates contained on the card (if supported by the middleware) are available as soon as they are inserted into the reader, via the certificate stores.
Note that it is the Smart Card Manager tool that transfers the certificates contained in the cards to the Windows certificate stores when the cards are inserted.
Applications using MacOS interfaces (CryptoTokenKit)¶
These applications (e.g. Safari) require no configuration. Each time a card is inserted, the OS identifies the CryptoTokenKit to be used, and the middleware intervenes automatically.
Applications using PKCS#11¶
The paths to be configured for applications using PKCS#11 are as follows:
For a 64-bit Windows application, or on a 32-bit machine:
C:\Program Files\Smart Card Middleware\bin\idoPKCS.dllFor a 32-bit Windows application on a 64-bit machine:
C:\Program Files (x86)\Smart Card Middleware\bin\idoPKCS.dllOn a MacOS machine:
/Library/SCMiddleware/libidop11.dylibOn a Linux machine :
/usr/lib/SCMiddleware/libidop11.so
Note: for Firefox, a plugin is installed to automatically configure PKCS#11 in the browser. The user simply needs to validate the execution of the plugin.
Web applications (SCWS)¶
Web applications do not require any configuration on the client workstation, on the part of the user.
It is up to the web application developer to include the appropriate WebAppCert in his application, to enable connection to the SCWS from client workstations.
WebAppCerts are generated by Idopte for each web application, based on the following information:
The origin(s) (URL base) from which the web application is to be accessed.
The web application’s public key (each web application has an RSA key pair with which a random-response authentication is performed, guaranteeing that the SCWS connection request is indeed made by the legitimate application).
This ensures that only approved web applications can access the middleware. Details of the authentication process between the web application and the SCWS are provided in the developer documentation available at https://www.idopte.com/doc_scws.php.
Configuring the AdSigner app¶
The middleware works in most configurations with AdSigner. However, it is possible that on some workstations the SlotNumber parameter (in the config.xml file) may need to be specifically adjusted.
In this case, you need to find the value of SlotNumber to put in the configuration file. For this, you can use the pkcs11-tool tool from the OpenSC suite.
After unzipping the file, run the following command, once the readers and cards are properly connected
pkcs11-tool –module C:WindowsSystem32iasP11.dll –list-slots
The slot to use contains the term “Signature”. The value to enter for SlotNumber in the AdSigner configuration is the hexadecimal number in parentheses. This number must be converted to decimal in the configuration file, for example, if the number found is 0xb, you must enter 11 in AdSigner.
In the following example, made with two readers and a card inserted in the second reader, the value found is 0x2, so SlotNumber must be set to 2 in AdSigner.
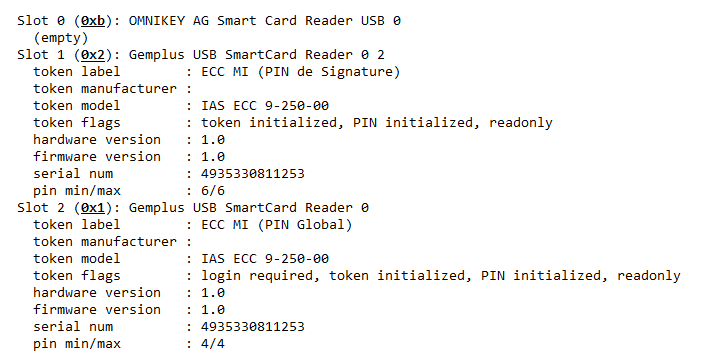
Example output from pkcs11-tool